The Cybersecurity Knowledge Architecture
In an ecosystem defined by rapid digital transformation and sophisticated asymmetric threats, cybersecurity has evolved from a technical necessity to a core business enabler. This hub serves as a comprehensive repository for security leaders, architects, and engineers, structured to guide organizations through the complexities of modern defense-in-depth strategies.
The landscape of information security is no longer static. With the dissolution of the traditional network perimeter, the rise of hybrid cloud infrastructures, and the weaponization of artificial intelligence, the defensive playbook must be rewritten. Organizations are now tasked with implementing Zero Trust architectures, ensuring rigorous data sovereignty under expanding global regulations (GDPR, CCPA), and shifting security left into the DevOps pipeline.
Below, we have organized critical intelligence into strategic clusters. Whether you are hardening a Kubernetes cluster, architecting a SASE (Secure Access Service Edge) solution, or establishing a robust Incident Response framework, this directory provides the foundational knowledge and advanced tactical guides required to secure your digital assets against next-generation adversaries.
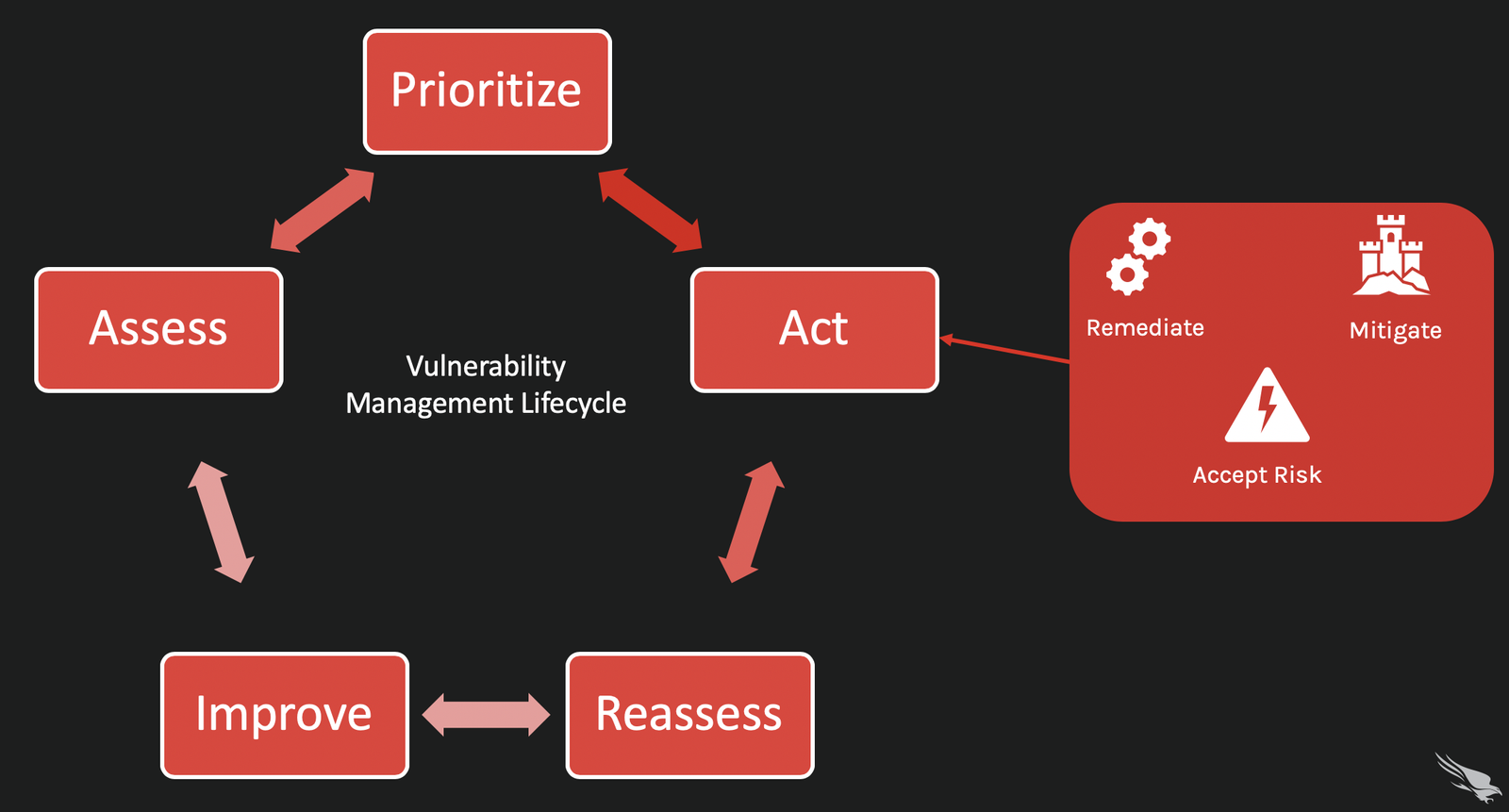
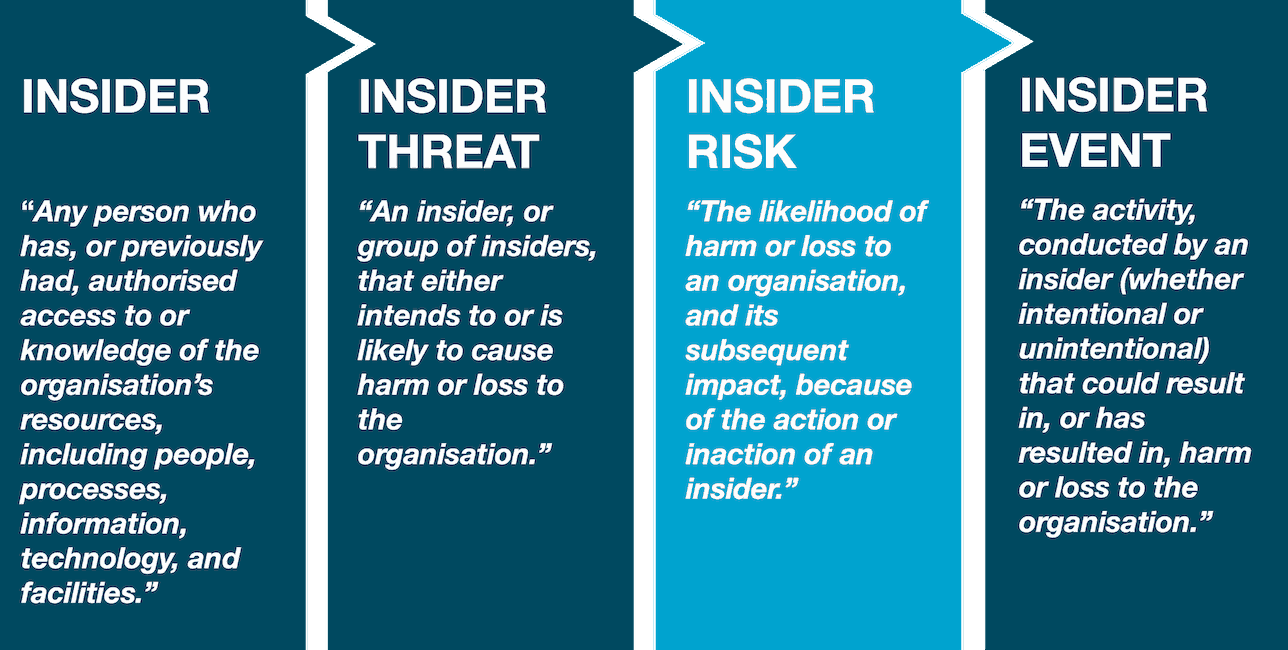
Threat Landscape & Vulnerability Management
Understanding the adversary is the first step in defense. The modern threat landscape is dominated by organized cybercrime syndicates and state-sponsored actors utilizing Advanced Persistent Threats (APTs). This section analyzes the anatomy of attacks, from the initial reconnaissance phase to data exfiltration, and details the methodologies required to manage vulnerabilities before they are exploited. We explore the shift from signature-based detection to behavioral analysis and heuristic monitoring.
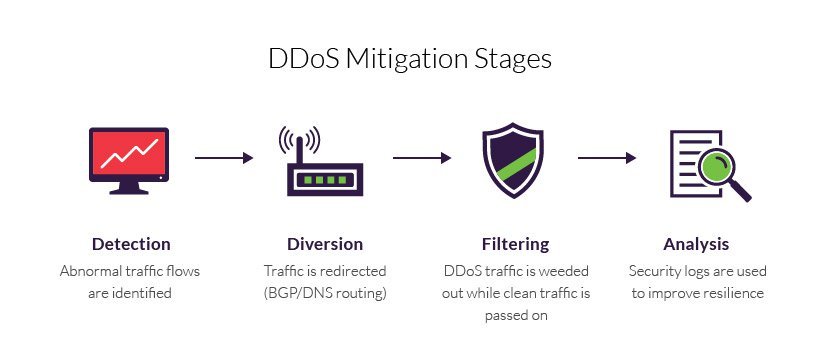
Network Security & Perimeter Defense
While the perimeter is dissolving, network security remains the backbone of enterprise infrastructure. This domain covers the transition from legacy MPLS networks to software-defined wide-area networks (SD-WAN) and Secure Access Service Edge (SASE) models. Topics include deep packet inspection, encrypted traffic analysis, and the deployment of Next-Generation Firewalls (NGFW) that are application-aware. Securing the data in transit is paramount to maintaining integrity and confidentiality.
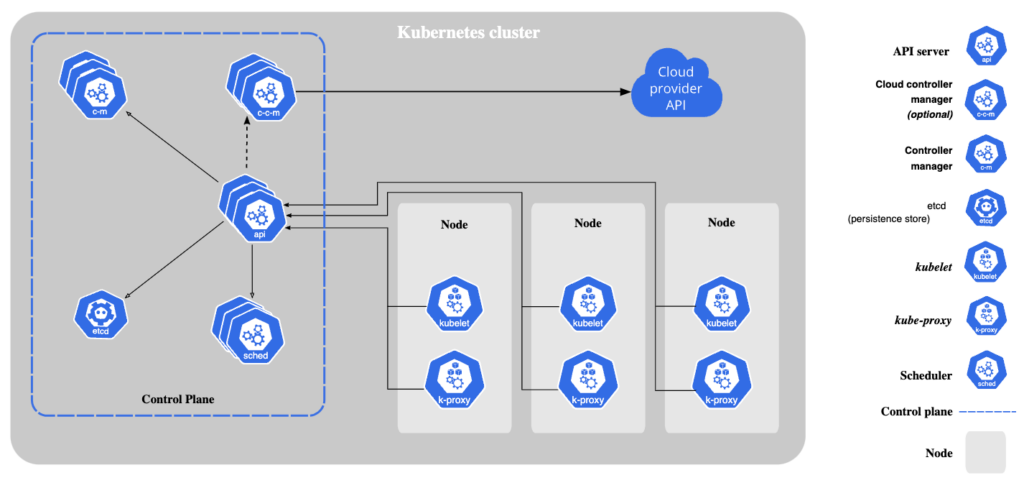
Cloud Security & Virtualization
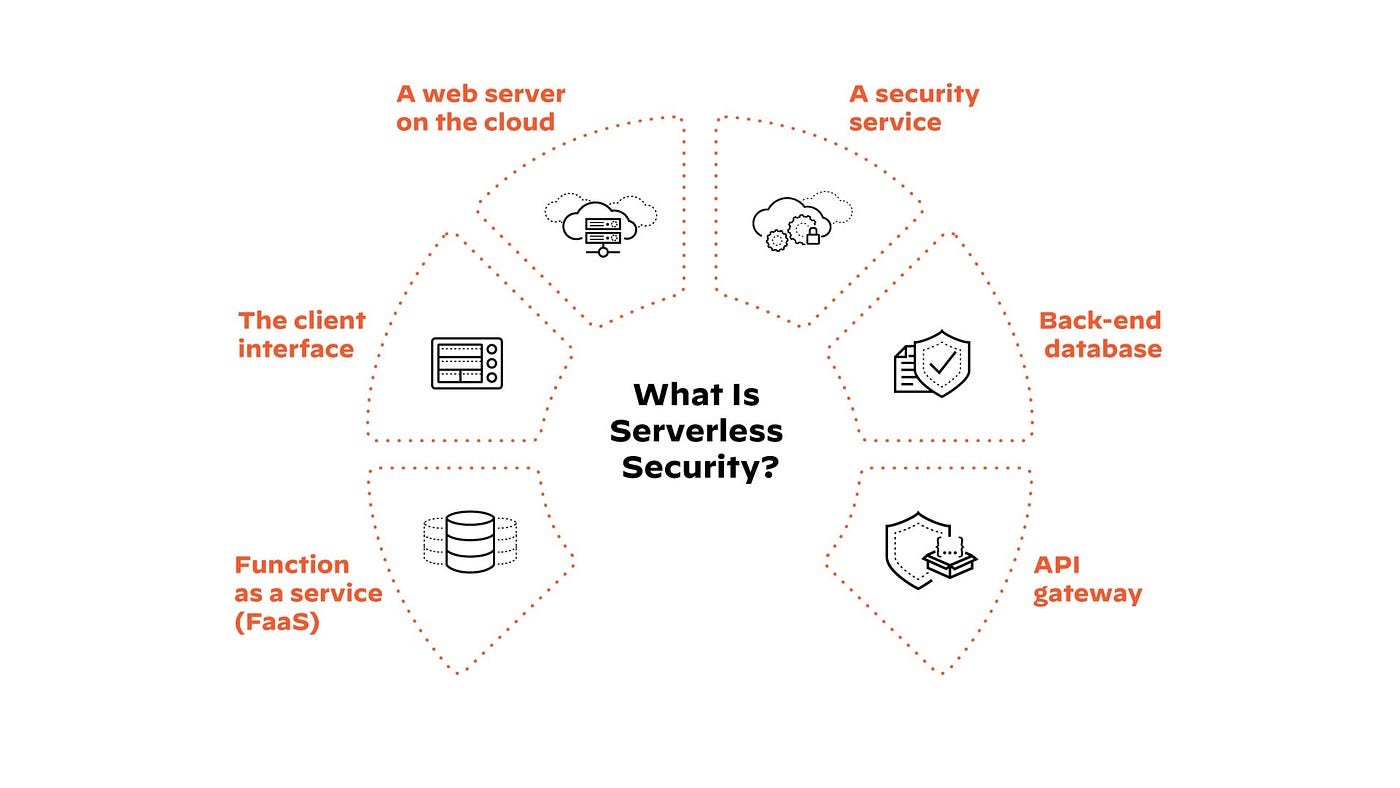
As workloads migrate to AWS, Azure, and Google Cloud, the Shared Responsibility Model becomes the governing principle of security. This section addresses the unique challenges of ephemeral infrastructure, including Cloud Security Posture Management (CSPM), Cloud Workload Protection Platforms (CWPP), and serverless security. We delve into the complexities of securing multi-cloud environments and the critical need for automated configuration auditing to prevent data leaks caused by misconfigured S3 buckets or open security groups.
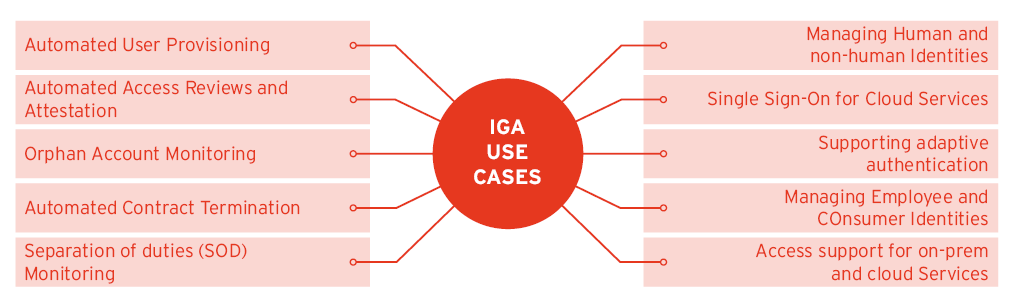
Zero Trust & Identity Management (IAM)
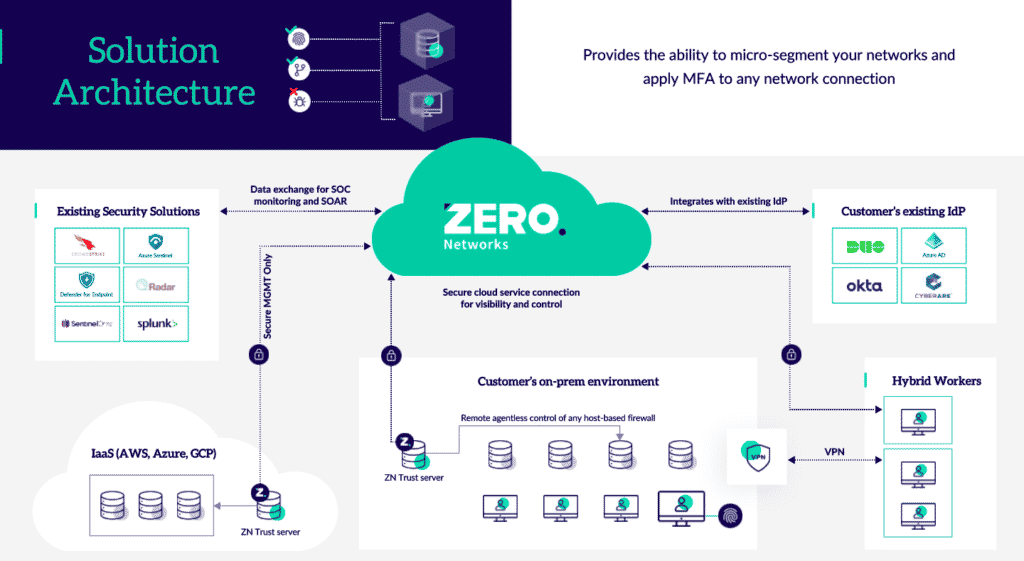
“Never Trust, Always Verify.” Zero Trust is not a product; it is a strategic initiative that eliminates implicit trust. This section explores the pillars of Zero Trust: Identity, Device, Network, Application, and Data. We provide detailed insights into Identity and Access Management (IAM), the implementation of Multi-Factor Authentication (MFA) everywhere, and the role of Privileged Access Management (PAM) in securing the “keys to the kingdom.”
SecOps, Incident Response & Forensics
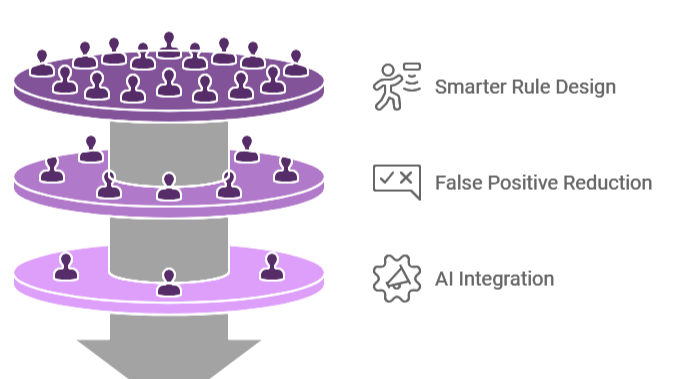
When prevention fails, detection and response become critical. Security Operations (SecOps) fuses security and IT operations to streamline the handling of alerts. This cluster covers the deployment of SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) tools to reduce alert fatigue. Furthermore, we discuss Digital Forensics fundamentals—how to preserve the chain of custody during an investigation and how to conduct root cause analysis after a breach.
DevSecOps & Application Security
Traditional “gatekeeper” security models impede the velocity of modern software development. DevSecOps integrates security controls directly into the CI/CD pipeline. This section explains how to implement Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) without breaking the build. We also cover API security in depth, addressing the vulnerabilities inherent in microservices architectures and the importance of Software Bill of Materials (SBOM) in supply chain security.
Frequently Asked Questions
Common inquiries regarding implementation, strategy, and career development in cybersecurity.
What is the difference between Red Teaming, Blue Teaming, and Purple Teaming?
These terms refer to organizational roles in security exercises. Red Teams are offensive security professionals who simulate real-world attacks to test defenses. They adopt the mindset of an adversary. Blue Teams are the defenders; they monitor systems, detect intrusions, and respond to incidents. Purple Teaming is a collaborative approach where Red and Blue teams work together openly. Instead of a surprise attack, the Red Team executes an exploit and immediately informs the Blue Team to help them tune their detection tools, maximizing the educational value of the exercise.
How does Zero Trust differ from traditional VPN security?
Traditional VPNs typically grant a user full access to a network segment once they are authenticated at the perimeter (the “castle and moat” model). If an attacker compromises VPN credentials, they can move laterally across the network. Zero Trust assumes the network is already compromised. It requires continuous verification of every request, regardless of origin. It utilizes “micro-segmentation” to ensure that users can only access the specific applications they need, not the entire network layer.
Why is the “Shift Left” approach important in DevSecOps?
“Shifting Left” means moving security testing to the earliest possible stages of the software development lifecycle (SDLC), rather than waiting for a security audit right before deployment. By identifying vulnerabilities (via SAST or SCA) during the coding phase, remediation is significantly cheaper and faster. It prevents security debt from accumulating and ensures that security is an inherent design feature rather than a bolt-on afterthought.
What is Ransomware-as-a-Service (RaaS) and why is it dangerous?
RaaS is a business model where ransomware developers sell or lease their malware to “affiliates” (hackers) in exchange for a cut of the ransom profits. This lowers the barrier to entry for cybercriminals, as affiliates do not need to know how to code sophisticated malware—they only need to know how to deploy it. This has led to an explosion in the volume and frequency of ransomware attacks globally.
How frequently should an organization perform a risk assessment?
At a minimum, a comprehensive risk assessment should be conducted annually. However, in dynamic environments, it should be event-driven. Assessments should be triggered by significant changes in the IT infrastructure (e.g., cloud migration), mergers and acquisitions, the introduction of new regulations, or following a major security incident. Continuous monitoring tools are now enabling “real-time” risk assessment in mature organizations.