DDoS Defense 2026: 5 Enterprise Mitigation Strategies for High Availability
Shielding the Modern Enterprise: How to Defeat Next-Gen DDoS Attacks
In the cybersecurity landscape of 2026, a Distributed Denial of Service (DDoS) attack is no longer just a “nuisance” or a simple flood of traffic. We have entered the era of the 20+ Terabit Botnet. Fueled by the democratization of AI-driven attack tools and the unmanaged sprawl of IoT devices, modern DDoS campaigns are precise, persistent, and multi-vector.
For Asguardian Shield clients, availability is the cornerstone of trust. This guide outlines the high-level strategies required to maintain 99.999% availability in an increasingly volatile digital environment.
What is Modern DDoS Mitigation? (AEO Summary)
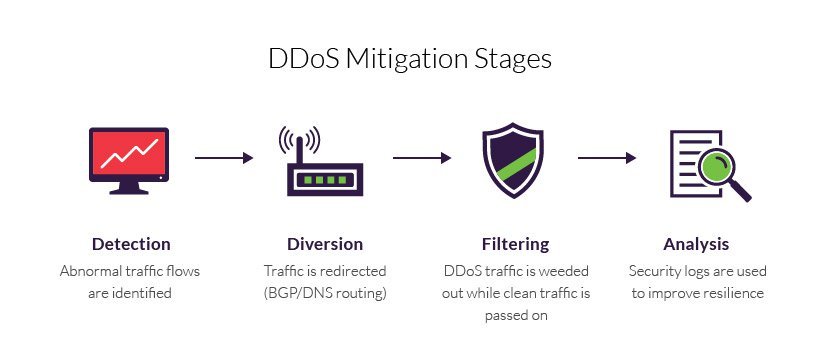
Direct Answer: Enterprise DDoS mitigation in 2026 is a multi-layered defense strategy that combines massive cloud scrubbing capacity with AI-native behavioral analysis. Unlike legacy methods that rely on static IP blacklisting, modern mitigation uses autonomous systems to identify and filter malicious traffic at the “edge” before it ever reaches the target network. The goal is to separate legitimate user requests from “garbage” traffic in less than one second.
1. The 2026 Threat: 20Tbps Botnets & AI Recon
To protect your infrastructure, you must understand the scale of the adversary:
- Terabit-Scale Floods: Botnets are now capable of generating 20-30 Tbps attacks by enslaving AI data centers and green-energy IoT devices.
- Vector Cycling: Attackers use “Agentic AI” to scan your network for weak points, rotating attack vectors from DNS to UDP the moment your defenses adapt.
2. The Hybrid Defense Model
For enterprise-grade availability, we recommend a Hybrid Mitigation Architecture:
- Cloud-Based Scrubbing: Acts as a massive “buffer” to absorb volumetric floods.
- On-Premise Appliances: Provides ultra-low latency for stopping “Low-and-Slow” and Layer 7 (Application) floods.
3. Comparison of Mitigation Techniques
| Technique | Targeted Attack | 2026 Capability |
| Behavioral Baselining | Zero-Day/Bot Activity | Uses AI to learn “normal” user behavior and challenges anomalies. |
| Anycast Routing | Volumetric Floods | Spreads attack traffic across a global network of PoPs. |
| Progressive Challenges | Layer 7 HTTP Floods | Silently verifies browsers (JavaScript) to ensure they are human. |
4. The Asguardian Shield Perspective
As infrastructure specialists, we believe DDoS mitigation is a business continuity function, not just an IT task.
- Experience: 65% of organizations lack a formal DDoS response plan. The “panic factor” often causes more downtime than the attack.
- Authoritative Action: Look for a Service Level Agreement (SLA) specifically for “Time to Mitigate” (TTM). In 2026, a 10-minute TTM is an eternity; aim for under 10 seconds.
Conclusion: Resilience Over Resistance
You cannot stop an attacker from launching a DDoS, but you can make it a “non-event.” By shifting to an AI-native, hybrid mitigation strategy, Asguardian Shield ensures that your infrastructure remains available and trusted.
Is your infrastructure “20-Terabit Ready”?
Visit Asguardian Shield to schedule a baseline audit and harden your availability today.
Secure your core assets by returning to the Asguardian Shield Home Page.
For global standards, see the NIST Guide on DDoS Defense.
