Micro-segmentation Guide 2026: Reducing Blast Radius with Zero Trust
Containing the Chaos: How Micro-segmentation Reduces the Blast Radius in 2026
In the legacy era of cybersecurity, we built high walls at the perimeter and assumed that everything inside was “trusted.” This created a catastrophic flaw: once an attacker breached the front door (via a single compromised laptop or a stolen credential), they had unfettered access to the entire data center. This “flat network” architecture is exactly how modern ransomware spreads, moving laterally from a marketing workstation to the production database in minutes.
In 2026, Asguardian Shield advocates for a total shift in philosophy. If a breach is inevitable, our goal is to ensure that it is contained. Micro-segmentation is the architectural solution that shrinks the “blast radius” of an attack to the smallest possible unit—often a single application, service, or workload.
What is Micro-segmentation? (Direct Answer)
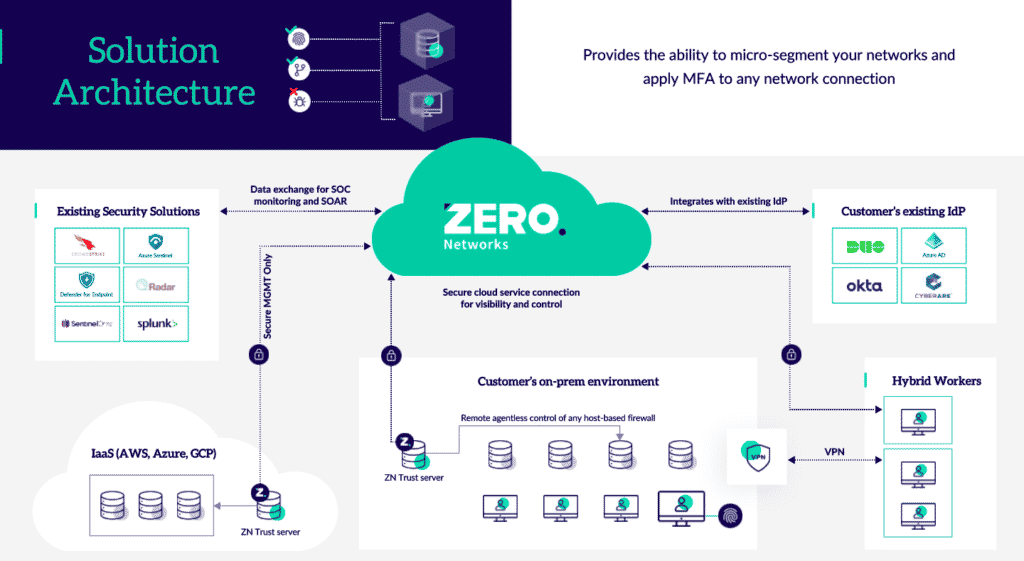
Summary: Micro-segmentation is a network security technique that enables security architects to logically divide the data center and cloud environments into individual, isolated security segments down to the workload level. Unlike traditional segmentation (which uses hardware firewalls to separate broad subnets), micro-segmentation uses Software-Defined Networking (SDN) and Host-Based Firewalls to control “East-West” traffic (server-to-server). In a 2026 Zero Trust model, micro-segmentation ensures that even if one segment is compromised, the attacker cannot move laterally to adjacent systems, effectively trapping the threat in a digital “clean room.”
1. Traditional vs. Micro-segmentation: The 2026 Comparison
To understand why micro-segmentation is the new standard, we must look at how it differs from the “castle and moat” strategies of the past.
| Feature | Traditional Network Segmentation | Modern Micro-segmentation |
| Enforcement Point | Edge Firewalls / Core Switches | Host-based Agents / Hypervisors / Sidecars |
| Traffic Direction | North-South (User to App) | East-West (App to App / Database) |
| Granularity | Coarse (VLANs / Subnets) | Fine (Workload / Process / Identity) |
| Policy Definition | IP Addresses & Ports | Metadata & Identity (e.g., env=prod) |
| Scalability | Rigid (Requires hardware changes) | Dynamic (Cloud-native / Automated) |
| Visibility | Blind to internal lateral flows | Full visibility of all inter-service traffic |
2. Reducing the Blast Radius: The Core Benefits
The primary value of micro-segmentation is Resilience through Isolation.
A. Instant Breach Containment
When an attacker gains a foothold in a micro-segmented environment, they find themselves in a “Zero Trust” enclave. If they try to scan for other servers or move from a Web Server to a Database, the micro-segmentation policy—which only allows specific, pre-approved flows—instantly blocks the attempt and triggers an alert.
B. Securing Legacy and OT Infrastructure
In 2026, many organizations still run “legacy” systems that cannot be patched. Micro-segmentation allows Asguardian Shield to “wrap” these vulnerable systems in a virtual security bubble, allowing them to communicate only with the one or two specific devices they need to function.
C. Compliance as a Side Effect
Regulations like GDPR, PCI-DSS, and HIPAA require the strict isolation of sensitive data. Instead of trying to secure your entire network to PCI standards, you can use micro-segmentation to “cordon off” the specific environment where credit card data lives, drastically reducing your audit scope and cost.
3. Implementation Strategies: How to Build Your Shield
A successful micro-segmentation rollout for Asguardian Shield clients follows three distinct technical approaches:
1. Host-Based (Agentic)
Lightweight agents are installed on every Virtual Machine (VM) or bare-metal server. These agents use the native firewall (like iptables or Windows Filtering Platform) to enforce rules.
- Benefit: Works across any cloud or data center; provides the deepest visibility into processes.
2. Network-Based (Fabric)
Security policies are enforced within the network fabric itself using SDN (Software-Defined Networking) controllers.
- Benefit: No agents required; great for IoT and medical devices that cannot support software installs.
3. Cloud-Native (Identity-Based)
Uses cloud-provider security groups and service mesh sidecars (like Istio) to enforce rules based on the Identity of the service rather than its IP address.
- Benefit: Essential for Kubernetes and serverless environments where IP addresses change every few seconds.
4. The 2026 Roadmap: A Phased Approach
Don’t try to segment 10,000 servers at once. Follow this mature roadmap to ensure business continuity:
- Phase 1: Visibility & Mapping: Use automated tools to “discover” how your applications currently talk to each other. You cannot secure what you don’t understand.
- Phase 2: Environment Isolation: Create broad “bubbles” to separate Production, Development, and Testing environments.
- Phase 3: Crown Jewel Protection: Identify your most sensitive assets (e.g., the ERP system) and build a “ring-fence” around them first.
- Phase 4: Automated Policy-as-Code: Integrate micro-segmentation into your CI/CD pipeline so that new applications are born with their security segments already defined.
5. Expert Pitfalls to Avoid
As specialists in enterprise architecture, we have observed two common mistakes:
- Over-complication: Trying to create “Nano-segments” for every tiny process too quickly leads to “Policy Bloat.” Start with logical tiers (Web → App → DB).
- The “Blind Side”: Forgetting about Non-Human Identities. Ensure your IGA Strategy is aligned so that bot and AI-agent traffic is also segmented.
Conclusion: Turning Your Network into an Asguardian Shield
Micro-segmentation is the definitive answer to the modern “Assume Breach” reality. By moving security controls from the edge of the network to the edge of the workload, you ensure that a single point of failure does not lead to total catastrophe. In 2026, isolation isn’t just a tactic—it’s your most powerful defense.
Is your lateral movement risk at an all-time high?
Contact Asguardian Shield for a Network Visibility & Segmentation Audit. We help you map your flows and build a resilient architecture that contains the most advanced threats.
- Complement your network isolation with our CISO’s Roadmap to Zero Trust Architecture.
- Review the industry-standard NIST Guide on Microsegmentation and Zero Trust.
