API Security 2026: Guide to Authentication & Rate Limiting
The API-First Fortress: Mastering Authentication and Rate Limiting for Microservices
In a microservices architecture, the “perimeter” is effectively everywhere. Every service-to-service call is a potential point of failure.1 The legacy approach of trusting internal traffic is no longer viable in 2026. At Asguardian Shield, we advocate for a Zero Trust API model, where every request—whether from a public-facing app or a hidden backend service—must be authenticated, authorized, and governed by strict traffic limits.
What is API Security?
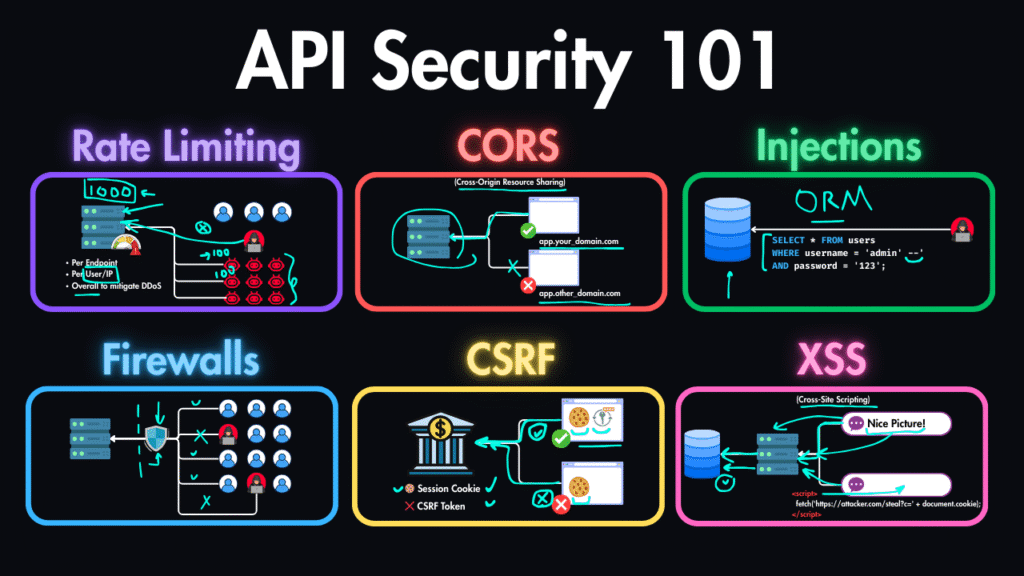
Direct Answer: API security is the practice of protecting Application Programming Interfaces (APIs) from unauthorized access, abuse, and exploitation.2 In a microservices environment, this focuses on two critical controls: Authentication, which ensures that the requestor (human or machine) is who they claim to be, and Rate Limiting, which prevents abuse by restricting the number of requests a client can make in a given timeframe. By 2026, these controls are typically enforced at the API Gateway or Service Mesh level to provide centralized governance across decentralized infrastructure.3
1. Modern API Authentication: Moving Beyond the Key
The days of a single, static X-API-KEY are over. Static keys are easily leaked and hard to rotate.4 In 2026, we utilize dynamic, token-based, and identity-centric models.5
A. OAuth 2.0 and OpenID Connect (OIDC)
For user-to-service authentication, OAuth2/OIDC is the gold standard.
- Scopes: Never grant “Full Access.” Use scopes to limit what a token can do (e.g.,
read:profilebut notdelete:account).6 - PKCE (Proof Key for Code Exchange): Mandatory for mobile and single-page apps to prevent authorization code interception.7
B. Mutual TLS (mTLS) for Internal Traffic
For service-to-service communication (East-West traffic), mTLS is the most secure option.
- How it works: Both the client and the server present certificates to each other.8 If the certificates aren’t signed by your internal Certificate Authority (CA), the connection is dropped.
- Implementation: Best managed through a Service Mesh like Istio or Linkerd to handle automatic certificate rotation.9
C. Securing JSON Web Tokens (JWT)
JWTs are convenient but dangerous if mismanaged.10
- Always Sign: Use asymmetric algorithms (RS256) rather than symmetric (HS256).
- Validate Everything: Check the expiration (
exp), issuer (iss), and audience (aud) claims on every request. - Short Lifespans: Tokens should last minutes, not days.11 Use Refresh Tokens for long-term sessions.
2. Advanced Rate Limiting Strategies
Rate limiting isn’t just about preventing a DDoS; it’s about protecting service availability and preventing automated “scraping” or “brute-forcing.”12
A. Fixed Window vs. Sliding Window
- Fixed Window: Resets at the start of every minute. (Vulnerable to “bursts” at the minute boundary).
- Sliding Window: Tracks the exact number of requests over the last 60 seconds. This is the 2026 standard for smooth, fair traffic management.
B. Tiered Rate Limiting
Not all users are equal.
- Anonymous Users: Very strict limits (e.g., 10 requests/min).
- Standard Users: Moderate limits (e.g., 100 requests/min).
- Enterprise/Partner Users: High limits (e.g., 1,000 requests/min).
C. Adaptive (Dynamic) Throttling
In 2026, AI-driven gateways analyze the Health of the Backend. If a microservice’s CPU is at 90%, the gateway automatically lowers the rate limits for non-essential traffic until the service recovers.
3. Comparison: Public vs. Internal API Security
| Feature | Public-Facing APIs | Internal Microservices |
| AuthN Method | OAuth2 / OIDC / Passkeys | mTLS / Service-to-Service JWT |
| Exposure | Exposed to Internet | Private Network (VPC/Mesh) |
| Threat Profile | Botnets, Brute-force, Scraping | Lateral Movement, Malicious Insiders |
| Rate Limiting | Strict (IP/User-based) | Resource-based (Service-to-Service) |
| Protection | WAAP / WAF | Micro-segmentation |
4. Strategic Roadmap for API Defense
At Asguardian Shield, we’ve found that API security is often forgotten in the rush to deploy. Follow this prioritized sequence:
- Phase 1: Discovery. Use your CSPM Tools to find “Shadow APIs” that aren’t behind your gateway.
- Phase 2: Centralized Auth. Move all authentication logic out of the microservice code and into the API Gateway or Service Mesh.
- Phase 3: Inventory Your Scopes. Audit your Identity Governance (IGA) to ensure API tokens are following the Principle of Least Privilege.
- Phase 4: Behavioral Monitoring. Use AI to detect “Low and Slow” scraping—where an attacker makes one request every 10 seconds to stay under the rate limit but eventually steals your entire database.
5. OWASP API Top 10: The Critical Checklist
Your security posture must specifically address the 2026 version of these risks:
- BOLA (Broken Object Level Authorization): Can User A access User B’s data by changing a
user_idin the URL?13 - BPLA (Broken Property Level Authorization): Can a user modify “read-only” fields like
is_adminvia a POST request? - Unrestricted Resource Consumption: This is where Rate Limiting saves your budget and your uptime.
Conclusion: Connectivity requires Control
APIs are the nervous system of the modern enterprise.14 Without robust authentication and intelligent rate limiting, that system is vulnerable to paralysis and data theft. By implementing a centralized, identity-first API strategy, Asguardian Shield ensures that your microservices remain connected, performant, and impenetrable.
Are your APIs exposed to credential stuffing or data scraping?
Contact Asguardian Shield for an API Security Audit. We’ll help you implement mTLS, harden your OAuth2 flows, and deploy adaptive rate limiting for 2026.
- Secure your APIs against larger floods with our Enterprise DDoS Mitigation Strategies.
- Review the latest OWASP API Security Top 10 Project for in-depth vulnerability descriptions.
