Automating CI/CD Security 2026: The DevSecOps Integration Guide
The DevSecOps Shift: Automating Security in the CI/CD Pipeline for 2026
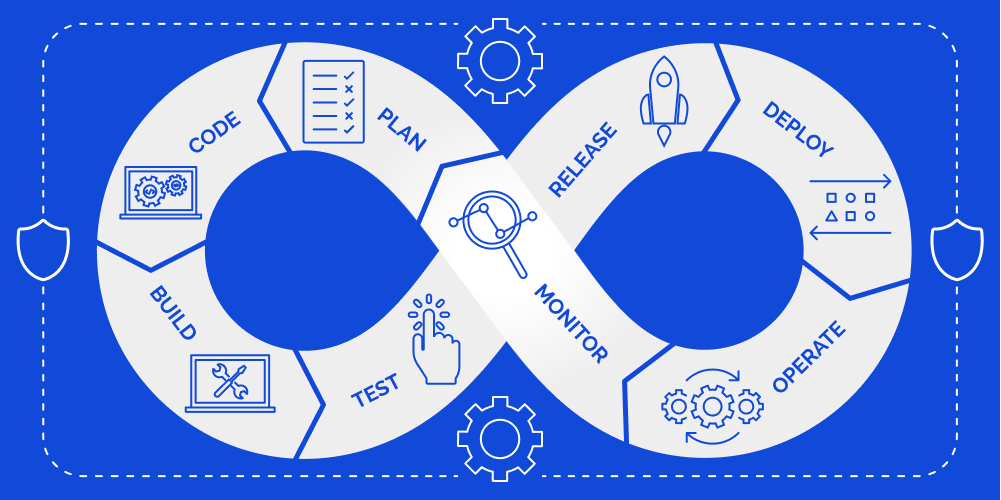
The traditional model of performing a security audit after code is written but before it is deployed has failed. In modern infrastructure, where Kubernetes Hardening and Serverless Functions define the landscape, security must be “Shifted Left.”
At Asguardian Shield, we view the CI/CD pipeline not just as a delivery mechanism, but as a continuous security enforcement engine. By automating security at every stage—from the first git commit to the final production deployment—you transform security from a “blocker” into a “quality gate.”
What is CI/CD Security Automation?
Direct Answer: CI/CD security automation is the practice of integrating automated security checks—such as SAST, DAST, SCA, and IaC Scanning—directly into the continuous integration and continuous deployment pipeline. The goal is to identify and remediate vulnerabilities early in the software development life cycle (SDLC). By using automated “Security Gates,” a pipeline can automatically reject code that contains critical vulnerabilities, leaked secrets, or non-compliant infrastructure configurations, ensuring only “Known Good” code reaches production.
1. The Four Pillars of Automated Pipeline Security
To build a resilient DevSecOps engine, your pipeline must automate four distinct types of analysis:
A. Static Application Security Testing (SAST)
SAST analyzes the source code before it is compiled. It looks for “code-level” flaws like SQL injection, buffer overflows, and insecure cryptographic implementations.
- 2026 Standard: Use Incremental SAST that only scans the “diff” (newly added code) to keep pipeline speeds high.
B. Software Composition Analysis (SCA)
In 2026, 90% of a modern application is made of third-party libraries. SCA identifies vulnerabilities in your dependencies (e.g., npm, pip, or maven packages).
- The Goal: Generate a Software Bill of Materials (SBOM) for every build to track “Transitive Dependencies” (the libraries your libraries use).
C. Dynamic Application Security Testing (DAST)
DAST tests the application while it is running. It interacts with the web interface or API to find vulnerabilities that only appear in a live state, such as authentication flaws or server misconfigurations.
- Integration: Integrate DAST with your WAF vs. WAAP strategy to verify that your edge protections are actually working.
D. Infrastructure as Code (IaC) Scanning
As infrastructure becomes code (Terraform, CloudFormation, Helm), it must be scanned for misconfigurations.
- Example: Automatically blocking a Terraform pull request that tries to launch an S3 bucket with public read access.
2. Implementing Security Gates: The “Fail-Fast” Model
Automation is meaningless if it doesn’t have the authority to stop a build. Asguardian Shield practitioners implement “Security Gates” with tiered thresholds.
| Pipeline Stage | Security Tool | Action on Failure |
| Commit | Secret Scanning | Block Merge: Prevent API keys from entering the repo. |
| Build | SAST / SCA | Warn: If Medium risk. Fail: If Critical/High risk. |
| Test | DAST / IAST | Fail: If unauthenticated endpoints are discovered. |
| Deploy | IaC Scanning | Block Deploy: If CSPM standards are violated. |
3. Protecting the Pipeline Itself: “Security OF the Pipeline”
While we focus on the code inside the pipeline, we must also secure the pipeline infrastructure. In 2026, “Pipeline Poisoning” is a major attack vector.
- Hardened Runners: Ensure build runners are ephemeral (destroyed after every build) and have no persistent access to production secrets.
- Signature Verification: Use Code Signing to ensure that the artifact built in Phase A is the exact same artifact deployed in Phase D, preventing “Man-in-the-Middle” tampering.
- Access Control: Apply Identity Governance (IGA) to your GitHub/GitLab/Jenkins instances. Who can change the pipeline script? This is often the weakest link.
4.Strategic Roadmap for DevSecOps
Transitioning to an automated model is a cultural journey. Follow this expert-led sequence:
- Phase 1: Visibility (No Blocking). Integrate SAST and SCA but don’t fail the build yet. Just provide the data to developers.
- Phase 2: Secret Scanning. Implement a hard block on any code containing plaintext secrets. This is a non-negotiable first win.
- Phase 3: The “Critical” Gate. Set the pipeline to fail only on “Critical” vulnerabilities with a known fix. This builds trust with development teams.
- Phase 4: Full Automation. Enable IaC scanning and automated DAST, integrating results into the developer’s native workflow (e.g., Jira or GitHub Issues).
5. Metrics: Measuring Pipeline Health
A successful DevSecOps implementation should be measured by these 2026 KPIs:
- MTTR (Mean Time to Remediate): How long it takes a developer to fix a vulnerability once the pipeline flags it.
- Vulnerability Density: The number of vulnerabilities per 1,000 lines of code.
- Build Failure Rate due to Security: A metric of how often the security gates are effectively stopping “bad” code.
- False Positive Rate: If your SAST tool flags too much noise, developers will ignore it. Aim for <5% noise.
Conclusion: Security at the Speed of Code
Automation is the only way to scale security in a decentralized, cloud-native world. By integrating security directly into the CI/CD pipeline, you ensure that every deployment is a “Known Good” state. At Asguardian Shield, we help you bridge the gap between “Dev” and “Sec,” turning your pipeline into your most powerful defensive asset.
Is your pipeline leaking secrets or pushing vulnerable code?
Contact Asguardian Shield for a DevSecOps Maturity Audit. We’ll help you automate your security gates and harden your delivery lifecycle for 2026.
- Align your pipeline security with your Kubernetes Hardening Strategy.
- Explore the OWASP DevSecOps Guideline for deep-dive technical standards.
