CSPM & Compliance 2026: The Enterprise Guide to Automated Cloud Security
From Chaos to Compliance: Mastering Cloud Security Posture Management (CSPM) in 2026
The cloud is a shifting landscape. Every minute, developers launch new S3 buckets, update IAM roles, and modify security groups across AWS, Azure, and Google Cloud. In this high-velocity environment, human oversight is impossible. Statistics show that over 90% of cloud breaches are caused not by sophisticated hackers, but by simple misconfigurations left behind during rapid deployment.
Cloud Security Posture Management (CSPM) is the solution to this “visibility gap.” At Asguardian Shield, we define CSPM as the central nervous system of your cloud defense—a platform that continuously scans, identifies, and remediates security risks before they can be exploited.
What is CSPM? (Direct Answer)
Summary: Cloud Security Posture Management (CSPM) is a category of security tools designed to automate the identification and remediation of risks across cloud infrastructures (IaaS, PaaS, and SaaS). By connecting directly to cloud APIs, CSPM tools compare your live configurations against industry benchmarks like CIS, NIST, and SOC 2. In 2026, CSPM has evolved into an Agentic AI model, where the system doesn’t just alert you to an open port; it autonomously evaluates the context and closes it in real-time.
1. Why Traditional Audits Fail in 2026
In the past, compliance was a “point-in-time” event. You ran a scan once a quarter, generated a PDF report, and spent weeks manually fixing errors. This approach is dead.
In 2026, compliance is Continuous.
- Ephemeral Assets: Containers and serverless functions live for seconds. If your scanner only runs once a day, it misses the risks these assets created.
- Identity Drift: Permissions “creep” over time as users are granted temporary access that is never revoked. CSPM identifies this Identity Drift instantly.
- Regulatory Velocity: With the introduction of the EU AI Act and updated GDPR mandates, manual tracking of regulatory changes is no longer feasible.
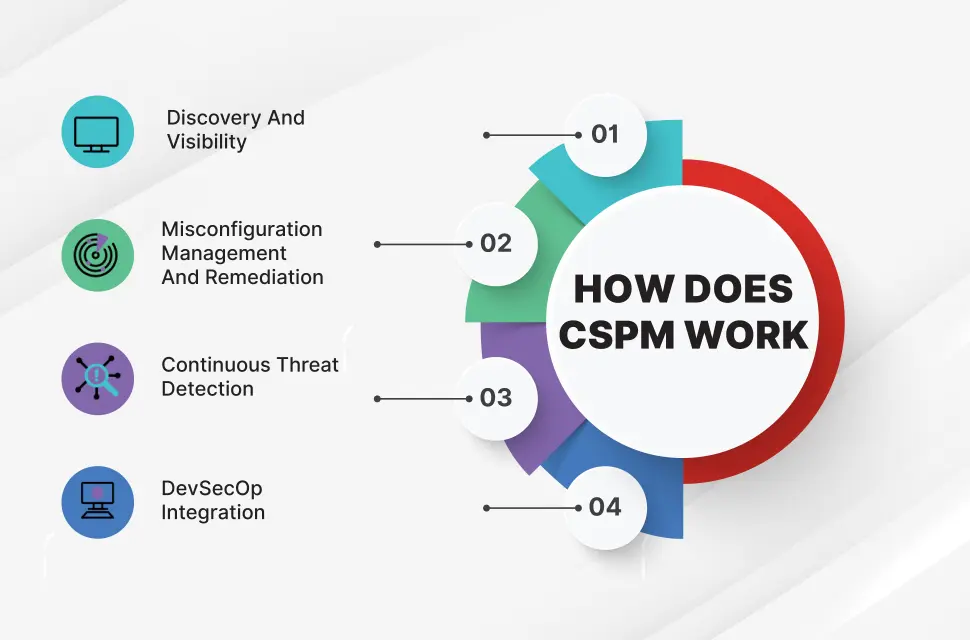
2. The Core Capabilities of Modern CSPM
For Asguardian Shield clients, a 2026-ready CSPM solution must provide more than just a list of red flags. It must provide Context.
A. Agentless Discovery and Visibility
Modern CSPM uses cloud-native APIs to gain a “God’s eye view” of every resource across every region without requiring you to install software (agents) on every server. This ensures 100% coverage with zero impact on performance.
B. Misconfiguration Management
CSPM looks for the “Low-Hanging Fruit” that attackers love:
- Unencrypted databases and storage buckets.
- Publicly accessible SSH or RDP ports.
- MFA (Multi-Factor Authentication) disabled on root accounts.
- Use of outdated TLS versions or weak ciphers.
C. Attack Path Analysis
This is the most critical advancement in 2026. Instead of showing you 1,000 disconnected alerts, CSPM uses graph technology to show you a Chained Risk.
Example: An unpatched vulnerability on a web server isn’t just a “High” risk. It becomes a “Critical” risk if that server also has an IAM role that can write to your production database.
3. CSPM vs. DSPM: Protecting the Data, Not Just the Box
A common question we receive is the difference between CSPM and Data Security Posture Management (DSPM).
| Feature | CSPM (Infrastructure) | DSPM (Data-Centric) |
| Focus | How the “container” is built. | What is inside the container. |
| Example | Is this S3 bucket public? | Does this bucket contain PII or Credit Cards? |
| Goal | Secure the configuration. | Secure the sensitive information. |
| 2026 Best Practice | Converged CSPM+DSPM: You cannot truly prioritize a configuration risk if you don’t know the value of the data it protects. |
4. Automating Compliance: From Alerting to Remediation
Governance in 2026 is about Guardrails, not just gatekeeping.
Step 1: Framework Mapping
CSPM tools come pre-loaded with “Policy Packs.” You select your requirement—say, HIPAA—and the tool automatically maps every cloud configuration check to a specific HIPAA control.
Step 2: Automated Evidence Collection
During an audit, you no longer need to take manual screenshots. Your CSPM provides a “Live Compliance Score” and an automated audit trail that serves as cryptographic proof of your security posture.
Step 3: Self-Healing Remediation
For high-risk, clear-cut errors (like an unencrypted disk), the CSPM can be set to Auto-Remediate. The moment the disk is launched, the CSPM detects the lack of encryption and triggers a script to encrypt it or shut it down immediately.
5. Implementation Roadmap for Asguardian Shield Clients
If you are starting your CSPM journey, follow this 2026 maturity model:
- Level 1: Visibility. Connect all cloud accounts (including Shadow IT) to a single dashboard.
- Level 2: Prioritization. Turn on “Contextual Risk Scoring” to filter out the noise and focus on the 5% of alerts that actually lead to data exposure.
- Level 3: Governance. Integrate your CSPM with your Mastering the Shared Responsibility Model strategy to clearly define who fixes what.
- Level 4: Full Automation. Move from “Manual Fixes” to “Policy as Code,” where non-compliant resources are automatically blocked at the deployment stage.
Conclusion: Visibility is Survival
In the 2026 threat landscape, you cannot protect what you cannot see. By implementing a robust Cloud Security Posture Management (CSPM) strategy, you transform your cloud from a sprawling, unmanaged liability into a hardened, compliant, and transparent asset.
Is your cloud compliance score falling behind?
Contact Asguardian Shield today for a multi-cloud posture audit. We help you automate your security so you can focus on your business.
- Strengthen your cloud foundation by reviewing our Shared Responsibility Model Guide.
- For industry-standard cloud benchmarks, see the CIS (Center for Internet Security) Foundations Benchmarks.
