Identity Governance & Administration (IGA) 2026: The Enterprise Strategy Guide
Governing the Human and Machine: The Evolution of Identity Governance & Administration (IGA)
In the 2026 digital landscape, identity has definitively replaced the network as the primary security boundary. However, simply enforcing access (IAM) is no longer enough. Organizations now face a “Governance Gap”—a growing sprawl of excessive permissions, orphaned accounts, and unmanaged service accounts that create a massive, invisible attack surface.
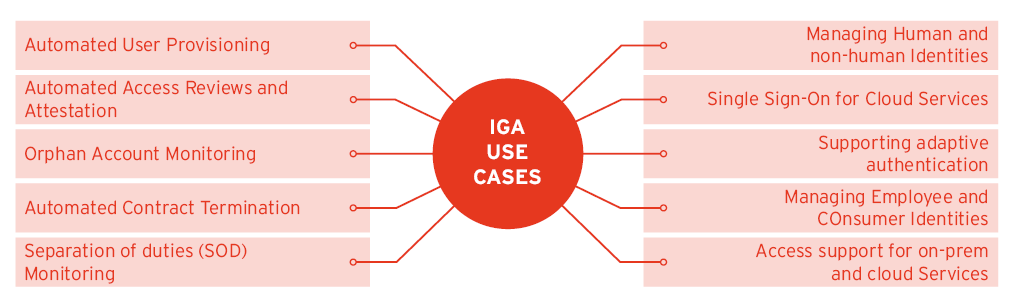
Identity Governance & Administration (IGA) is the strategic framework that closes this gap. While IAM asks, “Can this user log in?”, IGA asks the more important questions: “Should they have this access? Who approved it? Is it still necessary? And can we prove it to an auditor?”
At Asguardian Shield, we view IGA as the “System of Record” for identity, ensuring that trust is never assumed and access is always justified.
What is IGA? (Direct Answer)
Summary: Identity Governance and Administration (IGA) is a policy-based framework that manages the digital identity lifecycle and access rights across an entire organization. It combines Identity Administration (the “how”—onboarding, provisioning, and deprovisioning) with Identity Governance (the “why”—compliance, access reviews, and risk analytics). In 2026, IGA has expanded to include Non-Human Identities, providing the same level of oversight for AI agents, bots, and service accounts as it does for human employees.
1. IGA vs. IAM: Understanding the 2026 Distinction
A common strategic error is treating IAM and IGA as interchangeable. For a resilient infrastructure, you must understand their complementary roles.
| Feature | IAM (The Enforcement Layer) | IGA (The Governance Layer) |
| Primary Goal | Access: Getting the user in. | Compliance: Ensuring access is right. |
| Timeframe | Real-time (at login/request). | Lifecycle-based (periodic/ongoing). |
| Key Capability | SSO, MFA, Authentication. | Access Reviews, Role Mining, SoD. |
| Decision Maker | IT Admins / Automated Rules. | Business Managers / Compliance Officers. |
| Outcome | An active user session. | Audit evidence and risk reduction. |
2. The Core Pillars of a Mature IGA Strategy
To implement a high-performing IGA program for Asguardian Shield, you must focus on these four foundational pillars:
Pillar 1: Automated Lifecycle Management (Joiner-Mover-Leaver)
The most significant security risks come from “stale” access.
- Joiner: Automatically provision “Birthright” access based on job roles on day one.
- Mover: When an employee changes departments (e.g., from Finance to Marketing), the IGA system must automatically revoke old Finance permissions while granting new ones.
- Leaver: Instant, automated deprovisioning. In 2026, an “orphaned account” left active for even one hour is a liability.
Pillar 2: Access Certification and Reviews
IGA transforms the “Manager Review” from a rubber-stamping exercise into a risk-based decision.
- Continuous Certification: Instead of an annual “audit panic,” 2026 best practices use AI to flag high-risk entitlements for immediate review while automatically certifying low-risk, standard access.
Pillar 3: Segregation of Duties (SoD) Enforcement
SoD is the primary defense against internal fraud.
- The Policy: A single user should not be able to both “Create a Vendor” and “Approve a Payment.”
- The Enforcement: IGA identifies “Toxic Combinations” of permissions across different applications (e.g., SAP and Salesforce) and blocks them before they can be exploited.
Pillar 4: Entitlement Management & Role Mining
Instead of assigning thousands of individual permissions, IGA uses Role-Based Access Control (RBAC).
- Role Mining: The IGA system analyzes current access patterns to “mine” and suggest efficient roles, reducing “Permission Creep” and simplifying the user request process.
3. The 2026 Challenge: Governing Non-Human Identities
As we move into the “Agentic Era,” the fastest-growing identity category isn’t humans—it’s AI Agents, APIs, and Bots.
- The Problem: These identities often inherit the “Full Admin” privileges of their creators and operate 24/7 without oversight.
- The IGA Solution: In 2026, every AI agent must have a defined Owner and a Lifecycle. Your IGA platform should automatically deprovision an API key if the associated project is marked as “Closed” in your project management system.
4. Strategic Implementation Roadmap
At Asguardian Shield, we have found that IGA projects fail when they try to “boil the ocean.” Follow this expert-led sequence:
- Inventory First: Use a “Unified Identity Graph” to find all identities—including those in “Shadow IT” apps.
- Start with the “Leavers”: The highest ROI in IGA is automating the offboarding process. Stop the “access leakage” immediately.
- Define Business Roles: Work with department heads to define what a “Standard Sales Rep” actually needs. Move away from custom, one-off permissions.
- Integrate with SASE: Align your IGA policies with your SASE Architecture to ensure that identity-governed roles are enforced at the network edge.
5. Measuring Success: IGA Metrics That Matter
A successful IGA program should be measured by the reduction of risk and the increase in operational speed:
- Orphaned Account Rate: The % of active accounts with no associated active employee (Goal: <0.1%).
- Access Review Completion Time: How long it takes for managers to certify access.
- SoD Violation Count: Number of toxic permission combinations detected and blocked.
- Provisioning Time: How long it takes a new hire to get their first set of tools (Goal: <4 hours).
Conclusion: Identity is Governance
In the complex, multi-cloud infrastructure of 2026, you cannot secure what you do not govern. Identity Governance & Administration (IGA) is the foundation upon which Zero Trust is built. It provides the visibility, accountability, and automation required to turn identity from a liability into a competitive advantage.
Is your identity lifecycle still managed by spreadsheets?
Contact Asguardian Shield for an IGA Maturity Assessment. We help you move from manual reviews to automated, AI-driven governance that scales with your business.
- Combine your identity strategy with our CISO’s Roadmap to Zero Trust.
- For deep technical standards on role management, see the NIST Guide on Role-Based Access Control.
