Kubernetes (K8s) Hardening Guide 2026: Container Security & Cluster Defense
The Kubernetes Hardening Manifesto: Securing Production Clusters in 2026
Kubernetes has become the operating system of the modern cloud. However, its default configurations often prioritize ease of use over stringent security. In 2026, where supply chain attacks and “low-and-slow” lateral movement are the norm, securing K8s requires a multi-layered approach that addresses the control plane, the data plane, and the workloads themselves.
At Asguardian Shield, we treat K8s hardening as a continuous lifecycle. This guide distills the latest NSA, CISA, and CIS benchmarks into a practical framework for enterprise-grade container security.
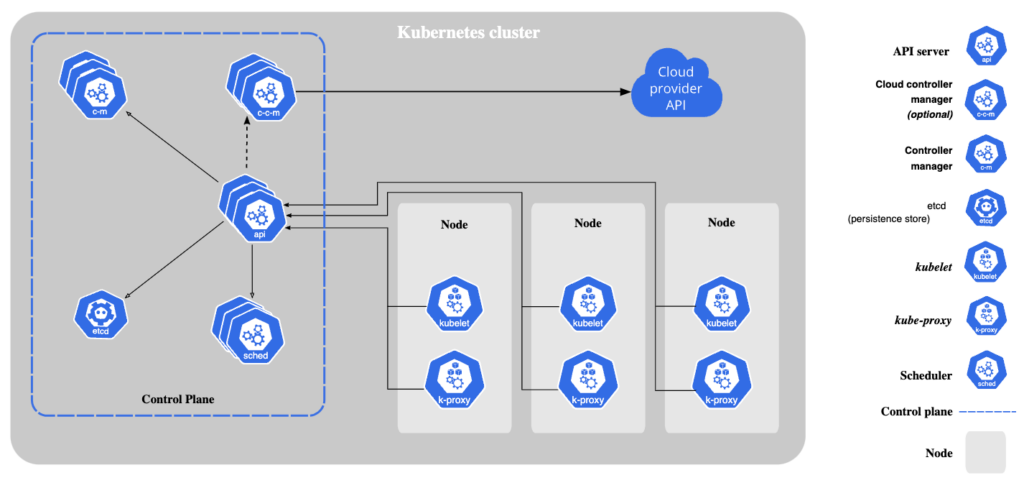
1. Hardening the Control Plane: The Brain of the Cluster
The control plane is the most critical target. If an attacker compromises the API server, they control the entire infrastructure.
A. Secure the API Server
- Disable Anonymous Access: Ensure
--anonymous-auth=falseis set. In 2026, K8s v1.34+ allows you to limit anonymous requests only to specific health endpoints like/healthz. - Restrict Access: The API server should never be exposed to the public internet. Use a private endpoint and secure it with a VPN or trusted jump box.
- Enforce TLS 1.3: Only allow modern, secure cipher suites for all control plane communication.
B. Protect the etcd Database
The etcd store contains every secret and configuration in your cluster.
- Encryption at Rest: Use an encryption provider (like AWS KMS or HashiCorp Vault) to encrypt
etcddata. - Mutual TLS (mTLS): Ensure
etcdonly communicates with the API server via verified certificates.
2. Authentication and RBAC (Least Privilege)
In 2026, identity is the primary perimeter. Most breaches occur because of over-privileged ServiceAccounts.
Best Practices:
- Eliminate
cluster-adminSprawl: Only a handful of human users should havecluster-adminrights. Use highly scopedRolesandRoleBindingsinstead ofClusterRoleswhenever possible. - Automated Token Management: Disable
automountServiceAccountTokenfor any pod that doesn’t need to talk to the API server. - Bound ServiceAccount Tokens: Leverage the 2025/2026 improvements that bind tokens to specific nodes, preventing an attacker from stealing a token and using it elsewhere in the cluster.
3. Network Security: The “Deny-By-Default” Era
By default, Kubernetes pods can talk to any other pod in the cluster. This is a dream for attackers seeking lateral movement.
Implement Network Policies
A modern hardening strategy requires a Deny-All policy as the baseline.
- Ingress/Egress Control: Explicitly define which pods are allowed to talk to each other.
- FQDN Filtering: Use a CNI like Cilium or Calico to restrict egress traffic to specific domain names (e.g., allow communication only to
api.stripe.com) to prevent data exfiltration. - Service Mesh Integration: For complex environments, use a service mesh (like Istio or Linkerd) to enforce mTLS between every single service automatically.
4. Workload & Container Hardening
The containers running inside your pods must be as lean and secure as possible.
A. The Move to “Distroless” and Hardened Images
In 2026, using a full Ubuntu or Debian image as a base is considered a security risk.
- Minimal Images: Use “Distroless” or “Alpine” images that contain only your application and its dependencies—no shell, no package manager.
- Non-Root Execution: Always set
runAsNonRoot: trueandrunAsUser: 10001in yoursecurityContext.
B. Pod Security Standards (PSS)
Replace the deprecated PodSecurityPolicies with the native Pod Security Admission (PSA).
- Enforce ‘Restricted’ Mode: At Asguardian Shield, we recommend the
restrictedprofile for all production namespaces. This prevents privileged containers, host network access, and privilege escalation by default.
5. Runtime Defense with eBPF
Static scanning is no longer enough. You must monitor what is actually happening inside the container during execution.
The Power of eBPF
Tools like Falco or Tetragon use eBPF (Extended Berkeley Packet Filter) to trace system calls with near-zero overhead.
- Anomaly Detection: Get alerted if a container suddenly starts an interactive shell, modifies a binary in
/bin, or opens an unexpected network connection. - Drift Prevention: Block any process that wasn’t part of the original container image.
6. Continuous Hardening Checklist 2026
| Task | Category | Frequency |
| CIS Benchmark Audit | Compliance | Weekly |
| Image Vulnerability Scan | Supply Chain | Every Build |
| RBAC Review | Identity | Monthly |
| Secret Rotation | Data Protection | 90 Days |
| mTLS Verification | Networking | Continuous |
Conclusion: Kubernetes as a Fortress
Hardening Kubernetes is not about a single configuration; it is about building a system where a failure in one layer is caught by another. By combining control plane encryption, strict RBAC, network microsegmentation, and eBPF runtime monitoring, you transform K8s from a vulnerable orchestrator into an Asguardian Shield.
Is your cluster configuration leaking secrets or allowing lateral movement?
Contact Asguardian Shield for a K8s Security Audit. We will help you align your architecture with the 2026 NSA/CISA hardening standards.
- For more on securing the underlying nodes, return to the Asguardian Shield Home Page.
- For the official government standards, download the NSA & CISA Kubernetes Hardening Guidance.
