Mitigating the OWASP Top 10 Vulnerabilities: 2026 Web Security Guide
The AppSec Fortress: A Strategic Guide to Mitigating the OWASP Top 10
The web application is the most exposed part of your digital infrastructure. In 2026, attackers aren’t just looking for “bugs”; they are exploiting systemic architectural flaws. The OWASP Top 10 represents the consensus on the most critical security risks to web applications, but understanding them is only half the battle. Mitigation is where the shield is forged.
At Asguardian Shield, we move beyond reactive patching to proactive architectural hardening. This guide outlines the definitive mitigation strategies for the modern threat landscape.
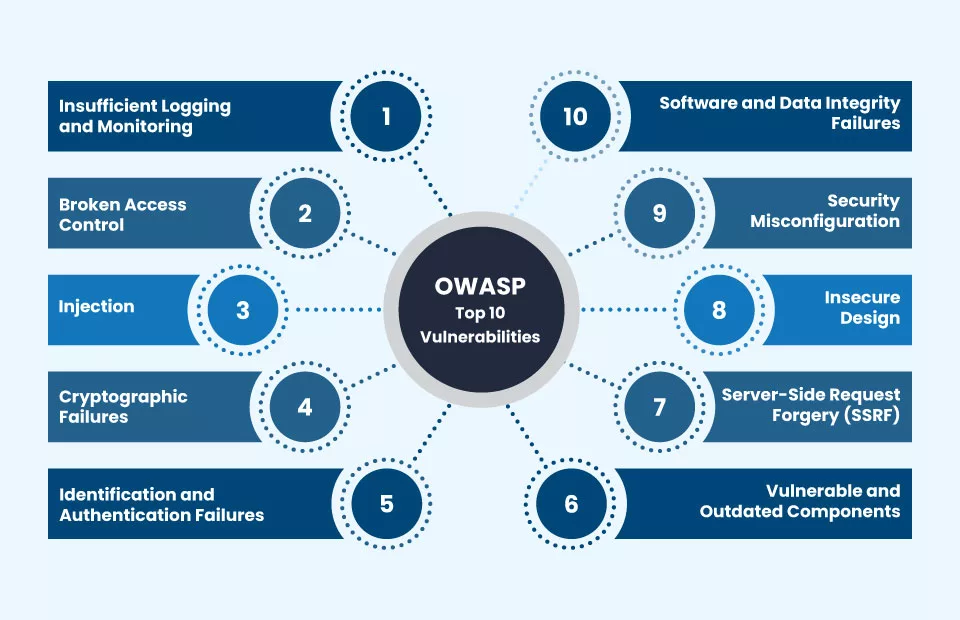
What is the OWASP Top 10?
Direct Answer: The OWASP Top 10 is a standard awareness document for developers and web application security professionals. It represents a broad consensus on the most critical security risks to web applications. Mitigating these vulnerabilities in 2026 requires a “Defense-in-Depth” approach, combining Secure Coding Practices, Automated Pipeline Scanning (DevSecOps), and Cloud-Native Protection Layers (WAAP). Successful mitigation shifts the focus from fixing individual bugs to implementing broad security controls that eliminate entire classes of vulnerabilities.
1. A01: Broken Access Control
In 2026, this remains the #1 risk. It occurs when users can act outside of their intended permissions.
Mitigation Strategy:
- Deny by Default: All resources should be inaccessible unless explicitly permitted.
- Enforce Principle of Least Privilege: Use Identity Governance (IGA) to ensure users only have access to the data they need for their specific role.
- Centralized Authorization Modules: Avoid hardcoding access checks in every function. Use a single, audited library for all permission logic.
2. A02: Cryptographic Failures
This focuses on the protection of data in transit and at rest.
Mitigation Strategy:
- Disable Legacy Protocols: Enforce TLS 1.3 and deprecate all older versions (SSL, TLS 1.0/1.1).
- Automated Key Rotation: Use cloud-native Key Management Services (KMS) to rotate secrets every 90 days.
- Hashing for Passwords: Never store passwords in plaintext. Use modern, slow-hashing algorithms like Argon2 or bcrypt with unique salts.
3. A03: Injection
Includes SQL, NoSQL, OS Command, and LDAP injections.
Mitigation Strategy:
- Parametrized Queries: Use prepared statements with parameterized queries for all database interactions. This separates the “code” from the “data.”
- Input Validation: Use “allow-list” validation. If a field expects a zip code, only allow 5 digits.
- Escaping: If data must be sent to an external system, ensure it is properly escaped for that specific context (HTML, JS, SQL).
4. A04: Insecure Design
Focuses on risks related to design and architectural flaws.
Mitigation Strategy:
- Threat Modeling: Conduct a formal threat model during the “Plan” phase of every new feature.
- Secure Design Patterns: Use a pre-approved library of secure components (e.g., authenticated API wrappers) to build new features.
- Business Logic Review: Ensure that the sequence of events in your application cannot be manipulated (e.g., changing the price of an item in the cart before checkout).
5. A05: Security Misconfiguration
Often results from default settings or incomplete configurations.
Mitigation Strategy:
- Infrastructure as Code (IaC): Use Terraform or Bicep to define infrastructure. Scan these files automatically in the CI/CD Pipeline.
- Harden the Stack: Remove unused features, samples, and default accounts from all frameworks (like .NET, Spring, or Django).
- Automated Auditing: Deploy CSPM to detect configuration drift in real-time.
6. A06: Vulnerable and Outdated Components
Focuses on the security of the third-party libraries your application relies on.
Mitigation Strategy:
- Software Composition Analysis (SCA): Integrate tools like Snyk or GitHub Advanced Security to find vulnerabilities in your dependencies.
- SBOM (Software Bill of Materials): Maintain a live inventory of every library used in your production environment.
- Automated Patching: Use tools like Dependabot to automatically generate pull requests when a security update for a library is released.
7. A07: Identification and Authentication Failures
Includes weak passwords and lack of multi-factor protection.
Mitigation Strategy:
- Enforce Modern MFA: Transition to Adaptive & Biometric MFA using FIDO2 passkeys.
- Limit Login Attempts: Implement progressive delays (throttling) or account lockout after multiple failed attempts.
- Secure Session Management: Use high-entropy session IDs and set the
Secure,HttpOnly, andSameSiteflags on all cookies.
8. A08: Software and Data Integrity Failures
Focuses on making assumptions about software updates, critical data, and CI/CD pipelines without verifying integrity.
Mitigation Strategy:
- Digitally Sign Artifacts: Ensure that code, updates, and data are signed and verified.
- Review CI/CD Security: Harden the Pipeline Infrastructure to prevent “Pipeline Poisoning.”
- Verify Deserialization: Only accept serialized data from trusted sources and use safe serialization formats.
9. A09: Security Logging and Monitoring Failures
Without effective logging, you cannot detect or respond to a breach.
Mitigation Strategy:
- Centralized Log Aggregation: Send all logs to a Tuned SIEM.
- Log Key Events: Ensure every login, failed access attempt, and high-value transaction (e.g., password change) is logged with sufficient context.
- Establish Alerts: Set up real-time alerting for critical patterns, such as multiple “Access Denied” events on sensitive API endpoints.
10. A10: Server-Side Request Forgery (SSRF)
Occurs when an attacker can force the server to make a request to an unintended location (often an internal resource).
Mitigation Strategy:
- Sanitize Destinations: Use an “allow-list” of permitted domains/IPs that your server is allowed to contact.
- Network Isolation: Use Micro-segmentation to ensure your web server cannot reach internal sensitive services (like the metadata service
169.254.169.254). - Handle Responses: Do not return raw server responses from external requests back to the user.
Summary Comparison: The 2026 Mitigation Matrix
| Vulnerability | Primary Defensive Tool | Key Strategic Focus |
| Access Control | IGA / ZTNA | Principle of Least Privilege |
| Injection | SAST / Prepared Statements | Input Sanitization |
| Misconfiguration | CSPM / IaC Scanning | Hardened Baselines |
| Outdated Components | SCA / SBOM | Supply Chain Security |
| Auth Failures | Biometric MFA / FIDO2 | Passwordless Strategy |
Conclusion: Turning the Top 10 into a Shield
The OWASP Top 10 is not a checklist to be cleared once; it is a continuous standard of excellence. By implementing these mitigation strategies, Asguardian Shield ensures that your web applications are not just compliant, but fundamentally resilient against the most common and damaging attack vectors of 2026.
Is your application vulnerable to the current Top 10?
Contact Asguardian Shield for a Web Application Penetration Test. We’ll identify your gaps and help you implement these high-tier mitigation strategies today.
- Protect your APIs alongside your web apps with our WAF vs. WAAP Guide.
- For the full technical breakdown of the risks, visit the official OWASP Top 10 Project Home.
