Securing Serverless Functions 2026: Lambda & Cloud Function Security Guide
The Serverless Security Paradigm: Protecting Lambda and Cloud Functions in 2026
Serverless computing—utilizing services like AWS Lambda, Azure Functions, and Google Cloud Functions—has revolutionized development velocity.2 By abstracting away the underlying server, organizations can scale infinitely. However, the common misconception is that “serverless” means “security-less.”
In the 2026 threat landscape, attackers have pivoted. They no longer target the operating system; they target the execution environment, the event source, and the over-privileged identity. At Asguardian Shield, we treat serverless security as an exercise in “Granular Defense,” where every function is its own micro-perimeter.
What is Serverless Security? (Direct Answer)
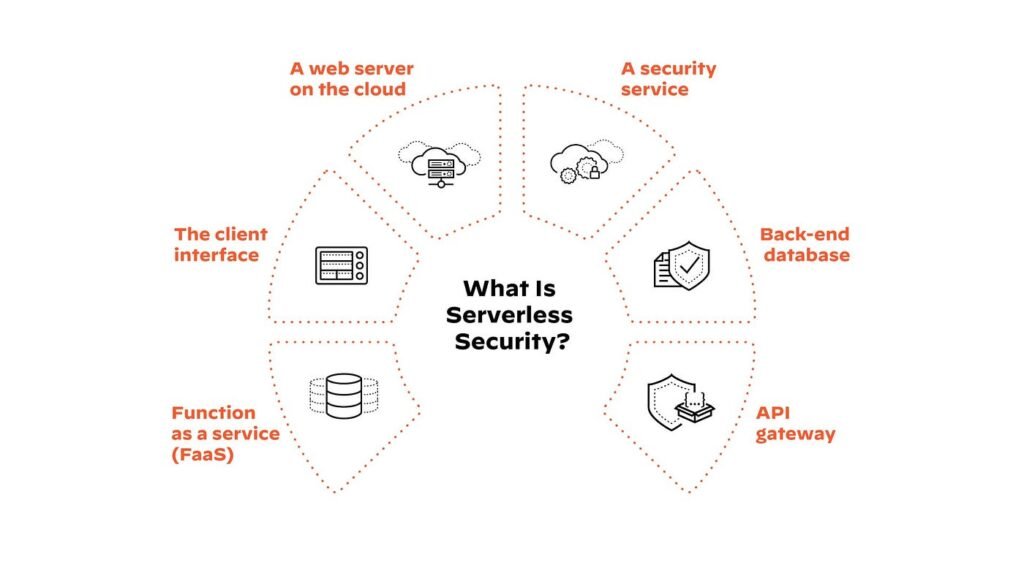
Summary: Securing serverless functions involves protecting the ephemeral execution environments where code runs in response to events.3 Unlike traditional application security, serverless defense focuses on Event Inspection, Identity-Centric Permissions (IAM), and API Security. Because these functions exist only for seconds, security must be baked into the code and the deployment pipeline rather than relying on traditional host-based firewalls or agents.
1. Defending Against the “Serverless Top 10”
The OWASP Serverless Top 10 remains the gold standard for understanding vulnerabilities. In 2026, two specific threats have become dominant:
A. Event Injection Attacks
In serverless, the “event” is the input. This could be an HTTP request via an API Gateway, a file upload to S3, or a message in a queue (SQS). If your code does not strictly sanitize these inputs, an attacker can inject malicious commands.4
- The Risk: An attacker uploads a file with a name like
; rm -rf /tmp/to trigger a shell command execution within the function. - The Defense: Never use system calls that invoke a shell. Use language-specific libraries for file and process management and validate all event schemas before processing.
B. Broken Function-Level Authorization
Because applications are now composed of hundreds of tiny functions, managing who can trigger which function is complex.
- The Risk: An internal function designed to “Delete User” is accidentally exposed to a public-facing API Gateway without an authorization check.
- The Defense: Implement a “Gateway-First” security model where every request is validated for a JWT or API key before it ever reaches the function.
2. The Principle of Least Privilege (IAM)
In 2026, identity is your only firewall. A common mistake is using a single, broad IAM role for all Lambda functions.
Best Practice: One Function, One Role
Every function should have its own dedicated IAM execution role.
- Granularity: If
Function_Aonly needs to write to an S3 bucket named “Logs,” do not give itS3:FullAccess. Give itS3:PutObjectrestricted specifically to that bucket’s ARN. - Secret Management: Never hardcode API keys or database credentials in environment variables. Use a service like AWS Secrets Manager or HashiCorp Vault, and grant the function the minimum permission needed to retrieve its specific secret at runtime.5
3. Runtime Security and Observability
Because you cannot install a traditional security agent on a serverless function, you must use “Function Wrappers” or library-level security.
A. Monitoring for Abnormal Behavior
Serverless functions are designed to be predictable. They do the same thing every time.
- Detecting Outliers: In 2026, AI-driven monitoring from Asguardian Shield can detect if a function that normally takes 200ms suddenly takes 5 seconds (potential data exfiltration) or if it suddenly starts making outbound connections to an unknown IP.
B. Managing “Cold Starts” and Poisoning
- Cold Start Risk: Attackers may attempt to “exhaust” your concurrency limits by flooding your functions, forcing cold starts and increasing costs (Denial of Wallet).
- Poisoning: If an attacker can manipulate the event source (like an S3 bucket or a DynamoDB stream), they can “poison” the function’s input repeatedly.
4. Comparing Serverless Security Layers
| Security Layer | Traditional App (VM/Container) | Serverless (Lambda/Functions) |
| Patching | You patch the OS and Kernel. | Cloud Provider patches the underlying host. |
| Perimeter | Firewall / VPC / WAF. | IAM / API Gateway / Event Filters. |
| Persistence | Attackers stay on the server. | Attackers must re-infect every execution. |
| Scaling | Manual or Auto-scaling groups. | Instant, infinite (Risk of cost spikes). |
| Blast Radius | Can be large (Full server access). | Small (Restricted to function scope). |
5. Implementation Roadmap: The 2026 Hardening Checklist
To secure your serverless architecture for the upcoming year, Asguardian Shield recommends this prioritized roadmap:
- Code Scanning (SCA): Since 90% of your function is likely third-party libraries, use Software Composition Analysis to find vulnerabilities in your
npmorpippackages.6 - API Gateway Hardening: Enable Throttling, WAF integration, and Request Validation at the gateway level.
- Timeout Limits: Set the shortest possible timeout for every function. If a function should take 2 seconds, set the timeout to 3 seconds. This prevents “long-running” malicious processes from staying active.
- VPC Integration: For functions that need to access internal databases, run them inside a private VPC with Security Groups that restrict traffic to only the required database ports.
Conclusion: Code is the New Perimeter
In the serverless era, the infrastructure is managed for you, but the integrity of the code and the logic of the event is entirely your responsibility. By applying strict IAM roles, rigorous input validation, and real-time observability, you can harness the power of serverless without exposing your enterprise to 2026-scale threats.
Are your Lambda functions over-privileged?
Contact Asguardian Shield for a Serverless Risk Assessment. We help you audit your IAM roles and implement runtime protection for your event-driven architecture.
- For more on securing the underlying infrastructure, see our guide on Kubernetes Hardening.
- Deepen your knowledge with the OWASP Serverless Top 10 Project.
