SIEM Tuning 2026: Strategies for Reducing False Positives & Alert Fatigue
Sharpening the Spear: SIEM Tuning Strategies for the 2026 Threat Landscape
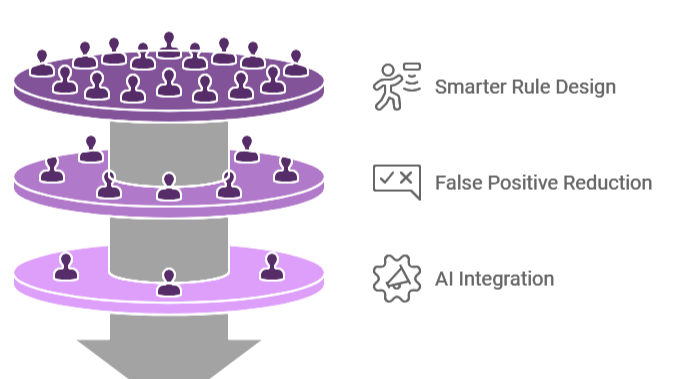
A SIEM is only as powerful as the logic behind its alerts. Many organizations treat their SIEM like a “digital hoarder,” ingesting every log source and enabling every default correlation rule. The result? A flood of thousands of low-value alerts that drown out actual indicators of compromise (IOCs). In 2026, “detection coverage” is no longer the metric of success; “Actionable Precision” is.
At Asguardian Shield, we view SIEM tuning as a continuous, cyclical evolution. By reducing false positives, we empower your analysts to spend their time hunting threats rather than closing tickets.
What is SIEM Tuning?
Summary: SIEM Tuning is the iterative process of refining detection rules, thresholds, and data filters to minimize False Positives (alerts that don’t represent a threat) and maximize the detection of True Positives (actual security incidents). In 2026, tuning has moved beyond static “if/then” rules to AI-Driven Suppression and Dynamic Thresholds. The goal of a tuned SIEM is to ensure that every alert triggered is “Actionable”—meaning it requires a specific, predefined response from the security team.
1. The Anatomy of a False Positive in 2026
To reduce false positives, you must first understand why they happen. Most noise in a 2026 SOC comes from three sources:
- Benign Anomalies: A scheduled server maintenance task that looks like a brute-force attack.
- Over-Broad Signatures: A rule that triggers on any “PowerShell execution” regardless of the user or script context.
- Non-Actionable Events: Alerts for successful logins from unusual locations that turn out to be approved business travel.
The Definition of “Noise”
If an alert triggers and the analyst says, “Oh, that’s just the vulnerability scanner again,” that alert is noise. It should be converted into a report for weekly review, not an active alert that opens a high-priority ticket.
2. Strategic Pillars for Reducing False Positives
Asguardian Shield recommends a four-pillar approach to SIEM optimization:
Pillar 1: Behavioral Baselining (UEBA)
Static thresholds (e.g., “Alert if >10 failed logins”) are easily bypassed or trigger too often.
- 2026 Standard: Use User and Entity Behavior Analytics (UEBA) to create a profile for every user. Instead of a hard number, the SIEM alerts when a user’s behavior is statistically significant from their 30-day norm.
Pillar 2: Contextual Enrichment
Raw logs lack the “Why.”
- The Strategy: Automatically enrich every alert with data from your IGA (to see user role), your CMDB (to see asset criticality), and Threat Intel feeds.
- Example: A failed login is “Low” risk. A failed login on a Crown Jewel server from a Tor Exit Node is “Critical.”
Pillar 3: Automated Suppression (SOAR)
Use your Incident Response Playbooks to handle the noise before a human sees it.
- Automation: If a known vulnerability scanner IP triggers a web attack alert, the SOAR platform should automatically verify the IP against the “Approved Scanner List” and close the ticket as “Informational.”
Pillar 4: Rule Decay & Decommissioning
Rules aren’t “forever.”
- Best Practice: Implement a “90-Day Review” for every detection rule. If a rule has a 0% True Positive rate over three months, it should be decommissioned or significantly rewritten.
3. Comparison: Static Rules vs. AI-Driven Tuning
| Feature | Legacy SIEM (Static) | Modern SIEM (AI-Tuned) |
| Alert Trigger | Hard-coded thresholds. | Dynamic, risk-based scores. |
| Logic Type | Signature-based (“If X then Y”). | Anomaly-based (“X is unusual for Y”). |
| Context | Single log source. | Cross-platform correlation. |
| Maintenance | Manual rule updates. | Self-learning behavioral models. |
| Analyst Impact | High Alert Fatigue. | High Precision / Focus. |
4. The 2026 Tuning Workflow: A 5-Step Cycle
To maintain a high-fidelity SIEM, Asguardian Shield practitioners follow this repeatable workflow:
- Ingestion & Normalization: Ensure data from NGFWs and Cloud logs are mapped to a common schema (like OCSF or ECS).
- Pilot Mode: New rules are deployed in “Learning Mode” (No alerts) for 14 days to observe their baseline trigger rate.
- Whitelisting & Filtering: Identify known-good service accounts and maintenance windows to exclude them from the rule.
- Production Deployment: Move the rule to “Active Alerting” once the False Positive rate is below 5%.
- Feedback Loop: Analysts tag every alert as “True Positive” or “False Positive.” The SIEM uses this feedback to “Self-Tune” future triggers.
[Image showing the alert feedback loop between the SOC Analyst and the SIEM’s ML engine]
5. Metrics that Matter
Stop measuring “Number of Alerts Handled.” Start measuring these efficiency metrics:
- False Positive Rate (FPR): (False Positives / Total Alerts) x 100. Target: <10%.
- Signal-to-Noise Ratio: The ratio of actionable incidents vs. informational logs.
- Mean Time to Triage (MTTT): How long it takes to decide if an alert is a real threat.
- Escalation Accuracy: How often a L1 analyst escalates an alert that turns out to be a real incident.
Conclusion: Visibility is Not Protection
In the 2026 landscape, a SIEM that sees everything but explains nothing is a liability. By committing to a rigorous program of SIEM Tuning, you transform your monitoring from a source of stress into a proactive, high-precision shield. At Asguardian Shield, we don’t just help you see the threats; we help you find them in the noise.
Is your security team drowning in alerts?
Contact Asguardian Shield for a SIEM Health Check and Tuning Audit. We’ll help you eliminate the noise and focus on the 2026 threats that truly matter.
- Integrate your tuned SIEM with our Effective Incident Response Playbooks.
- Review the MITRE ATT&CK Framework to align your detection rules with real-world adversary tactics.
